Targeted cyberattacks on the defense sector recorded in Ukraine via a popular messenger.
19.03.2025
1948

Journalist
Shostal Oleksandr
19.03.2025
1948
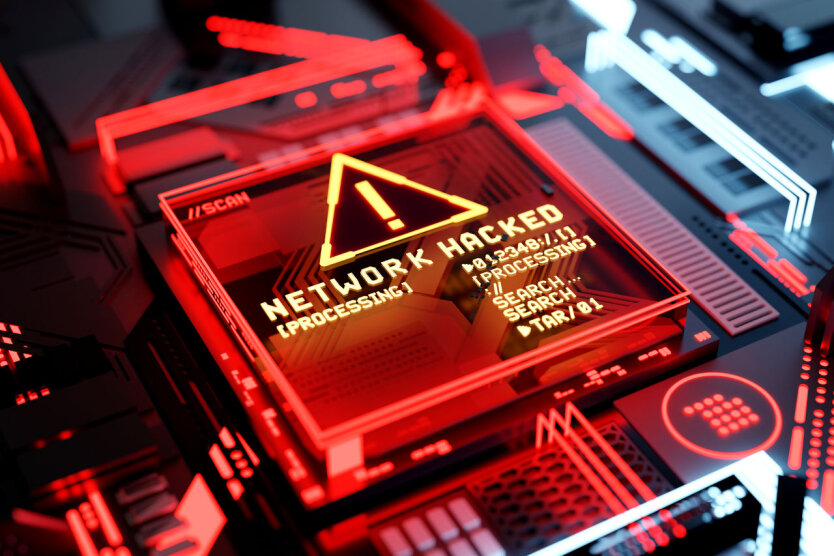
The CERT-UA team has detected cyberattacks on employees of the defense industry and the Armed Forces of Ukraine.
In March 2025, messages containing reports were found in the Signal messenger. Some messages were sent from individuals with compromised accounts to increase trust.
Typically, these archives contain a .pdf file and an executable file named DarkTortilla. DarkTortilla is a crypter/loader used to launch the remote control program Dark Crystal RAT (DCRAT).
'It should be noted that this activity has been tracked under the identifier UAC-0200 since at least the summer of 2024. Meanwhile, starting in February 2025, the content of the bait messages relates to UAVs, electronic warfare means, etc. The use of popular messengers, both on mobile devices and computers, significantly expands the attack surface, including by creating uncontrolled (in terms of protection means) channels for information exchange,' - CERT-UA reported.
Read also
- The General Staff responded to Russia's statement about a breakthrough in Dnipropetrovsk
- Ukrainians warned about a new massive attack from the Russian Federation: Kyiv and 8 other regions at risk
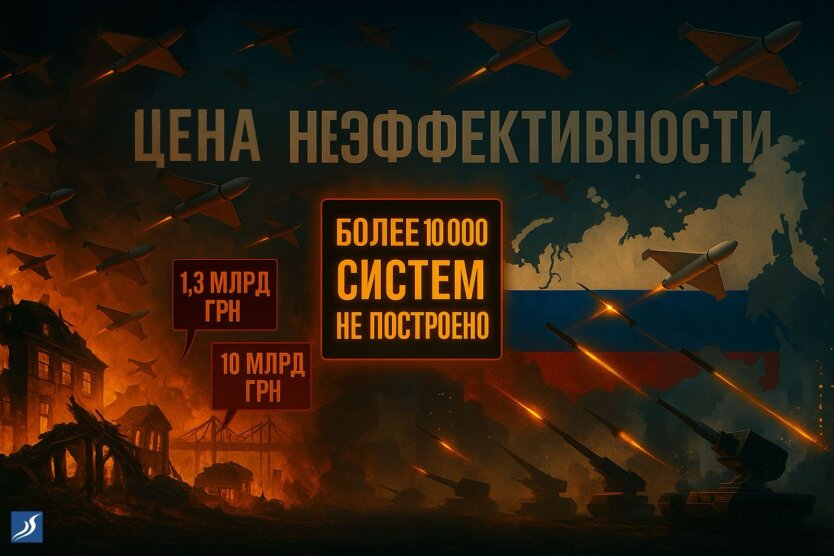
- The Cost of Inefficiency: Large-Scale Russian Attacks Require Large-Scale Organizational Responses from Ukraine
- War may come to us: the head of the Czech Republic issued a troubling warning
- Zelensky: The USA unexpectedly sent missiles intended for Ukraine to another country
- Zelensky said where Trump sent the 20 thousand missiles promised by Biden